A few days ago, PrivacySharks reported on the LinkedIn leak, in which a hacker posted 700m LinkedIn records for sale on RaidForums. It seems the hacker is not done with exploiting LinkedIn as he has updated the LinkedIn records, which now stand at a whopping 1B. Not only this, he has added a new file full of the email addresses and passwords of LinkedIn users.
We reached out to LinkedIn for verification and received this official statement from Leonna Spilman:
“While we’re still investigating this issue, our initial analysis indicates that the dataset includes information scraped from LinkedIn as well as information obtained from other sources. This was not a LinkedIn data breach, and our investigation has determined that no private LinkedIn member data was exposed. Scraping data from LinkedIn is a violation of our Terms of Service, and we are constantly working to ensure our members’ privacy is protected.”
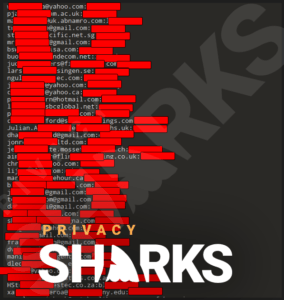
The new leak now consists of 300m new data records and has been categorized by users’ geo-locations, job titles, and educational backgrounds. User TomLiner, who is behind the leak, has included screenshots as evidence for each file. We have viewed these images and can confirm that the leaked data contains, but is not exclusive to, the following:
- Names (first and last)
- Email addresses
- Street addresses
- Cities
- States
- Zipcodes
- Phone numbers
- Websites
- LinkedIn profiles
- Company names
- Job titles
- Fax numbers
- Email and password combinations
- LinkedIn connections
Some of the files are larger than 19,000,000 KB, indicating just how much data has been scraped.
What’s unique about this compared to the previous leak is the smaller file, which contains passwords.
Does this include data from the previous leak?
Since the user behind this is the same individual linked to the 700m data leak, it’s safe to assume that most of the data is the same as that exposed previously. Initial investigations into the 500m and 700m LinkedIn record data leaks found that the data was scraped from public LinkedIn profiles and other websites.
As we know, LinkedIn commented on the alleged 700m data records leak, stating that it was not a security breach since no private LinkedIn member data was exposed and the scraping of publicly available information on its site is not a breach.
However, LinkedIn passwords were not a part of the previous leak. The fact that these are now being sold is worrying and could potentially put many LinkedIn accounts at risk.

Is the data actually from LinkedIn?
Leaked LinkedIn records amounting to 1B is a massive number. It’s definitely a troubling figure if the data is from LinkedIn members’ accounts. However, as claimed by LinkedIn in its previous statements, this data wasn’t solely scraped from the employment-based platform; some of the data has been obtained from other websites and telemarketing sets.
How many users have been affected by the leak?
A quick look at LinkedIn’s ‘About’ page informs us that the website currently has 756 million members.
Therefore, if we assume that every LinkedIn user’s information is included in this leak, there are around 250 million records that may come from duplicate users. This time around, the scraper has made it easier for others to sort the data by title, country, company, and even phone numbers.
A report from Threatpost has revealed how some LinkedIn users are already being attacked by scammers. A refined database of 88k business owners exposed by the 700m leak has been posted on RaidForums, and many of these business owners had changed jobs on LinkedIn within the past 90 days. It’s incredibly easy to see how an attacker could easily exploit a new business owner’s full email inbox and get them to click on a phishing link.
Therefore, we expect this new leak to have similar, if not worse, consequences for many LinkedIn users. Since LinkedIn is reliant upon users keeping their profile details updated, it’s likely that all of the scraped data is up-to-date and could be exploited by scammers and hackers.
What should LinkedIn users do?
Now that we know that email addresses and passwords have been exposed, we recommend that every LinkedIn user changes their password as a safety precaution. Whether or not your password is part of the leak, you should change it and create new passwords for any accounts where you have reused it.
Using a password manager will help you to create a strong password that isn’t easily cracked. However, if you don’t want to pay for a password manager subscription, make sure you create unique passwords consisting of no less than 15 characters.
Data leaks are also a general reminder of the fact that you should practice good internet safety. As well as creating strong passwords for all online accounts, use burner email addresses where possible and make sure you have antivirus software and a VPN installed on all of your devices.
References
Threatpost: https://threatpost.com/linkedin-data-scrape-victims-targeted-attackers/167473/

Hi, I'm Madeleine. I'm a British writer with a global background, currently based in the UK.
I have always been interested in the online world and how it connects people worldwide. My keen interest in the internet led me to ...
Read more about the author